Thứ Năm, 30 tháng 10, 2008
CCNA lab
CCNA Certification
 The Cisco CCNA network associate certification validates the ability to install, configure, operate, and troubleshoot medium-size routed and switched networks, including implementation and verification of connections to remote sites in a WAN. This new curriculum includes basic mitigation of security threats, introduction to wireless networking concepts and terminology, and performance-based skills. This new curriculum also includes (but is not limited to) the use of these protocols: IP, Enhanced Interior Gateway Routing Protocol (EIGRP), Serial Line Interface Protocol Frame Relay, Routing Information Protocol Version 2 (RIPv2),VLANs, Ethernet, access control lists (ACLs)
The Cisco CCNA network associate certification validates the ability to install, configure, operate, and troubleshoot medium-size routed and switched networks, including implementation and verification of connections to remote sites in a WAN. This new curriculum includes basic mitigation of security threats, introduction to wireless networking concepts and terminology, and performance-based skills. This new curriculum also includes (but is not limited to) the use of these protocols: IP, Enhanced Interior Gateway Routing Protocol (EIGRP), Serial Line Interface Protocol Frame Relay, Routing Information Protocol Version 2 (RIPv2),VLANs, Ethernet, access control lists (ACLs)
* 2 Router Configuration
* 3 Examine the Router
* 4 Copy to a TFTP server
* 5 Copy from TFTP server
* 6a Clear the backup config
* 6b Saving the backup configuration
* 7 Copy to NVRAM
* 8 Initial router configuration
* 9 Initial Switch Configuration
* 10 RIP routing
* 11 IGRP routing
* 12 Create Accesslist
* 13 IPX Access List Security
* 14 IPX router configuration
* 15 IPX SAP filtering
* 16 Limitting VTY address
* 17 Load 2600 OS
* 18 Navigating the IOS
* 19 Password recovery
* 20 Telnet to a remote Router
CCNA4U.TK Update dayly(hot news)
I will reply all the comments at the end of day(GMT+7)
(Email: quocvuong.it @ gmail.com)
To :Thank you very much
- nguyenkietvan
- Piotr
23/10/2008:
Update:
CCNA1 FINAL
24/10/08
Update:
CCNA4 Module 4 100%
CCNA4 MODULE 5 100%
30/10:
Update: CCNA3 FINAL (add 4 new questions)
CCNA3 FINAL 91.8 %
13/11/08
Thank Kthien very much
Thứ Tư, 29 tháng 10, 2008
CCNA Drag and Drop SIM Question
Question:
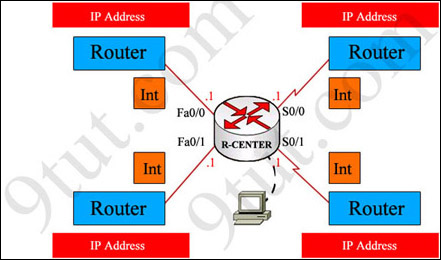
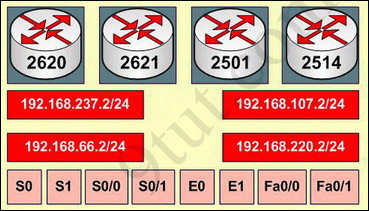
You have been hired by Specialty Hardware Incorporated to document the layout of the network. Complete the following tasks:? Complete the network topology shown in the graphic by dragging the labels below with the appropriate router types, interface types, and IP addresses to the graphic . Find the information you need by using the router console attached to the R-CENTER router.
Answer and explanation:
This is the simplest lab question in four labs you see in the real CCNA exam. First we should identify the types of these routers by using the show cdp neighbors command:
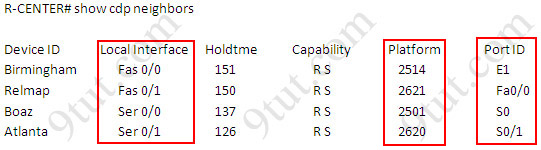
There are 3 columns we should pay more attention to:
+ Local Interface: the interface on the device you are using "show cdp neighbors" command. In this case it is the interface of R-CENTER router
+ Platform: the platform of neighbor device
+ Port ID: the neighbor device's port or interface on which the CDP packets are multicast
From the exhibit, the "Local Interface", "Platform" and "Port ID" columns, we can identify where these four routers should be placed and their corresponding associated ports
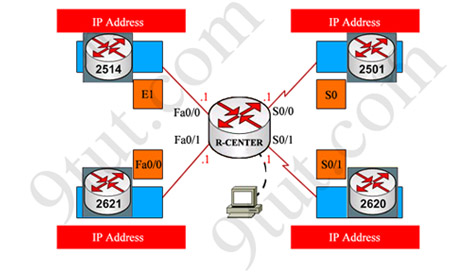
Finally, use the show running-config command to find out the ip addresses of four interfaces on R-CENTER

And we can easily assign corresponding ip addresses to four neighbor routers, which are on the same network with R-CENTER router's interfaces
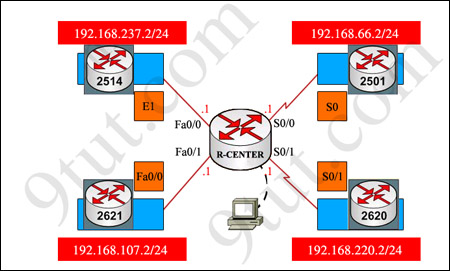
Please remember in the real CCNA Exam the routers' types, ip addresses and interfaces may be different! So make sure you understand how it works.
www.ccna-4.blogspot.com
Chủ Nhật, 26 tháng 10, 2008
CCNA-V4-S4-Final

http://www.ccna4u.info
DOWNLOAD
CCNA4 FINAL 100/100
ALL CCNA4 FINAL
94%
1. A technician has been asked to run Cisco SDM one-step lockdown on the router of a customer. What will be the result of this process?
Traffic is only forwarded from SDM-trusted Cisco routers.
Security testing is performed and the results are saved as a text file stored in NVRAM.
The router is tested for potential security problems and any necessary changes are made.
All traffic entering the router is quarantined and checked for viruses before being forwarded.
2. Refer to the exhibit. A network administrator is trying to configure a router to use SDM but it is not functioning correctly. What could be the problem?
The username and password are not configured correctly.
The authentication method is not configured correctly.
The HTTP timeout policy is not configured correctly.
The vtys are not configured correctly.
3. Refer to the exhibit. How is the TCP/IP configuration information specified by the default-router and dns-server commands made available?
The TCP/IP information is forwarded to a 10.0.1.3 to be supplied to DHCP clients.
The TCP/IP information is used by DHCP clients that are configured to request a configuration from R1.
The TCP/IP information is supplied to any DHCP client on the network connected to the FastEthernet 0/0 interface of R1.
The TCP/IP information is applied to each packet that enters R1 through the FastEthernet 0/0 interface that are hosts on the 10.0.1.0 /24 network except packets from addresses 10.0.1.2, 10.0.1.16, and 10.0.1.254.
4. What is a major characteristic of a worm?
malicious software that copies itself into other executable programs
tricks users into running the infected software
a set of computer instructions that lies dormant until triggered by a specific event
exploits vulnerabilities with the intent of propagating itself across a network
5. Refer to the exhibit. What can be concluded from the exhibited output of the debug ip nat command?
The 10.1.1.225 host is exchanging packets with the 192.168.0.10 host.
The native 10.1.200.254 address is being translated to 192.168.0.10.
The 192.168.0.0/24 network is the inside network.
Port address translation is in effect.
6. A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why Company A reports higher download speeds than Company B?
Company B has a higher volume of POTS voice traffic than Company A.
Company B shares the conection to the DSLAM with more clients than Company A.
Company A only uses microfilters on branch locations.
Company A is closer to the service provider.
7. Refer to the exhibit. Which statement correctly describes how Router1 processes an FTP request entering interface s0/0/0, destined for an FTP server at IP address 192.168.1.5?
It matches the incoming packet to the access-list 201 permit any any statement and allows the packet into the router.
It reaches the end of ACL 101 without matching a condition and drops the packet because there is no access-list 101 permit any any statement.
It matches the incoming packet to the access-list 101 permit ip any 192.168.1.0 0.0.0.255 statement, ignores the remaining statements in ACL 101, and allows the packet into the router.
It matches the incoming packet to the access-list 201 deny icmp 192.168.1.0 0.0.0.255 any statement, continues comparing the packet to the remaining statements in ACL 201 to ensure that no subsequent statements allow FTP, and then drops the packet.
8. Refer to the exhibit. Which two conclusions can be drawn from the output shown? (Choose two.)
This network is experiencing congestion.
The Frame Relay connection is in the process of negotiation.
Data is not flowing in this network.
The network is discarding eligible packets.
The DLCI is globally significant.
9. A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
Configure DHCP and static NAT.
Configure dynamic NAT for ten users.
Configure static NAT for all ten users.
Configure dynamic NAT with overload.
10. Refer to the exhibit. Company ABC expanded its business and recently opened a new branch office in another country. IPv6 addresses have been used for the company network. The data servers Server1 and Server2 run applications which require end-to-end functionality, with unmodified packets that are forwarded from the source to the destination. The edge routers R1 and R2 support dual stack configuration. What solution should be deployed at the edge of the company network in order to successfully interconnect both offices?
a new WAN service supporting only IPv6
NAT overload to map inside IPv6 addresses to outside IPv4 address
a manually configured IPv6 tunnel between the edge routers R1 and R2
static NAT to map inside IPv6 addresses of the servers to an outside IPv4 address and dynamic NAT for the rest of the inside IPv6 addresses
11. Refer to the exhibit. You are a network administrator who has been tasked with completing the Frame Relay topology that interconnects two remote sites. How should the point-to-point subinterfaces be configured on HQ to complete the topology?
HQ(config-subif)#frame-relay interface-dlci 103 on Serial 0/0/0.1
HQ(config-subif)#frame-relay interface-dlci 203 on Serial 0/0/0.2
HQ(config-subif)#frame-relay interface-dlci 301 on Serial 0/0/0.1
HQ(config-subif)# frame-relay interface-dlci 302 on Serial 0/0/0.2
HQ(config-subif)#frame-relay map ip 172.16.1.1 103 broadcast on Serial 0/0/0.1
HQ(config-subif)#frame-relay map ip 172.16.2.2 203 broadcast on Serial 0/0/0.2
HQ(config-subif)#frame-relay map ip 172.16.1.1 301 broadcast on Serial 0/0/0.1
HQ(config-subif)#frame-relay map ip 172.16.2.2 302 broadcast on Serial 0/0/0.2
12. An established company has recently transitioned from outsourced LAN support to a completely in-house staff. The outsourcing company is no longer in business, so no records are available. There are many user complaints about application speed and availability. What two considerations apply to this situation? (Choose two.)
A network utilization baseline should quickly reveal application availability.
A period of 24 to 48 hours should provide a sufficient baseline to track normal network activity.
It is easier to start with monitoring all available data inputs on application servers, and then fine-tune to fewer variables along the way.
The initial baseline results have little relevance to current values after the network has been modified or grown in usage.
When it is practical, network administrators should attempt to automate the collection of performance data and stay away from manual collection.
Creating a network baseline data helps determine device thresholds for alerting.
13. Which combination of Layer 2 protocol and authentication should be used to establish a link without sending authentication information in plain text between a Cisco and a non-Cisco router?
PPP with PAP
PPP with CHAP
HDLC with PAP
HDLC with CHAP
14. An administrator is unable to receive e-mail. While troubleshooting the problem, the administrator is able to ping the local mail server IP address successfully from a remote network and can successfully resolve the mail server name to an IP address via the use of the nslookup command. At what OSI layer is the problem most likely to be found?
physical layer
data link layer
network layer
application layer
15. When configuring a Frame Relay connection, what are two instances when a static Frame Relay map should be used? (Choose two.)
when the remote router is a non-Cisco router
when the remote router does not support Inverse ARP
when the local router is using IOS Release 11.1 or earlier
when broadcast traffic and multicast traffic over the PVC must be controlled
when globally significant rather than locally significant DLCIs are being used
16. Which three statements are true about creating and applying access lists? (Choose three.)
Access list entries should filter in the order from general to specific.
One access list per port per protocol per direction is permitted.
Standard ACLs should be applied closest to the source while extended ACLs should be applied closest to the destination.
There is an implicit deny at the end of all access lists.
Statements are processed sequentially from top to bottom until a match is found.
The inbound keyword refers to traffic entering the network from the router interface where the ACL is applied.
17. Which technology would provide the highest bandwidth connections between company sites at the lowest cost?
broadband Internet site-to-site VPN connections
satellite based network connections
dedicated point-to-point circuits
Frame Relay PVCs
18. Refer to the exhibit. This serial interface is not functioning correctly. Based on the output shown, what is the most likely cause?
improper LMI type
interface reset
PPP negotiation failure
unplugged cable
19. What three statements describe the roles of devices in a WAN? (Choose three.)
A CSU/DSU terminates a digital local loop.
A modem terminates a digital local loop.
A CSU/DSU terminates an analog local loop.
A modem terminates an analog local loop.
A router is commonly considered a DTE device.
A router is commonly considered a DCE device.
20. A network administrator is instructing a technician on best practices for applying ACLs. Which suggestion should the administrator provide?
Named ACLs are less efficient than numbered ACLs.
Standard ACLs should be applied closest to the core layer.
ACLs applied to outbound interfaces are the most efficient.
Extended ACLs should be applied closest to the source that is specified by the ACL.
21. Refer to the exhibit. Branch A has a Cisco router. Branch B has a non-Cisco router set for IETF encapsulation. After the commands shown are entered, R2 and R3 fail to establish the PVC. The R2 LMI is Cisco, and the R3 LMI is ANSI. The LMI is successfully established at both locations. Why is the PVC failing?
The PVC to R3 must be point-to-point.
LMI types must match on each end of a PVC.
The ietf parameter is missing from the frame-relay map ip 10.10.10.3 203 command.
The PVCs at R2 use different encapsulation types. A single port can only support one encapsulation type.
22. Which statement is true regarding wildcard masks?
The wildcard mask and subnet mask perform the same function.
The wildcard mask is always the inverse of the subnet mask.
A "0" in the wildcard mask identifies IP address bits that must be checked.
A "1" in the wildcard mask identifies a network or subnet bit.
23. Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the DC office of ABC Company to the
MAC address of the
MAC address of the DC router
192.168.1.25
192.168.1.26
DLCI 100
DLCI 200
24 .A company is looking for a WAN solution to connect its headquarters site with four remote sites. What advantage would dedicated leased lines provide to the customer compared to a shared Frame Relay solution?
lower cost
lower latency and jitter
variable bandwidth capacity
fewer physical router interfaces
25. Refer to the exhibit. RIPv2 has been configured on all routers in the network. Routers R1 and R3 do not receive RIP routing updates. On the basis of the provided configuration, what should be enabled on router R2 to remedy the problem?
proxy ARP
CDP updates
SNMP services
RIP authentication
26. What are the symptoms when the s0/0/0 interface on a router is attached to an operational CSU/DSU that is generating a clock signal, but the far end router on the point-to-point link has not been activated?
show controllers indicates cable type DCE V.35. show interfaces s0/0/0 indicates serial down, line protocol down.
show controllers indicates cable type DCE V.35. show interfaces s0/0/0 indicates serial up, line protocol down.
show controllers indicates cable type DTE V.35. show interfaces s0/0/0 indicates serial up, line protocol down.
show controllers indicates cable type DTE V.35. show interfaces s0/0/0 indicates serial down, line protocol down.
27. Which statement about a VPN is true?
VPN link establishment and maintenance is provided by LCP.
DLCI addresses are used to identify each end of the VPN tunnel.
VPNs use virtual Layer 3 connections that are routed through the Internet.
Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
28. Refer to the exhibit. Partial results of the show access-lists and show ip interface FastEthernet 0/1 commands for router R3 are shown. There are no other ACLs in effect. Host A is unable to telnet to host B. Which action will correct the problem but still restrict other traffic between the two networks?
Apply the ACL in the inbound direction.
Apply the ACL on the FastEthernet 0/0 interface.
Reverse the order of the TCP protocol statements in the ACL.
Modify the second entry in the list to permit tcp host 192.168.10.10 any eq telnet .
29. Refer to the exhibit. What happens if the network administrator issues the commands shown when an ACL called Managers already exists on the router?
The commands overwrite the existing Managers ACL.
The commands are added at the end of the existing Managers ACL.
The network administrator receives an error stating that the ACL already exists.
The commands will create a duplicate Managers ACL containing only the new commands being entered.
30. Which three statements accurately describe a security policy? (Choose three.)
It creates a basis for legal action if necessary.
It defines a process for managing security violations.
It defines acceptable and unacceptable use of network resources.
The remote access policy is a component of the security policy that governs acceptable use of e-mail systems.
It is kept private from users to prevent the possibility of circumventing security measures.
It provides step-by-step procedures to harden routers and other network devices.
31. Refer to the exhibit. The link between the CTRL and BR_1 routers is configured as shown in the exhibit. Why are the routers unable to establish a PPP session?
The clock rate must be 56000.
The usernames are misconfigured.
The IP addresses are on different subnets.
The clock rate is configured on the wrong end of the link.
The CHAP passwords must be different on the two routers.
Interface serial 0/0/0 on CTRL must connect to interface serial 0/0/1 on BR_1.
32. What effect would the Router1(config-ext-nacl)# permit tcp 172.16.4.0 0.0.0.255 any eq www command have when implemented inbound on the f0/0 interface?
All TCP traffic is permitted, and all other traffic is denied.
The command is rejected by the router because it is incomplete.
All traffic from 172.16.4.0/24 is permitted anywhere on any port.
Traffic originating from 172.16.4.0/24 is permitted to all TCP port 80 destinations.
33. What can a network administrator do to recover from a lost router password?
use the copy tftp: flash: command
boot the router to bootROM mode and enter the b command to load the IOS manually
telnet from another router and issue the show running-config command to view the password
boot the router to ROM monitor mode and configure the router to ignore the startup configuration when it initializes
34. A router in a Frame Relay network needs to forward a message received from a host. What two methods does the router use to identify the correct VC to forward the message? (Choose two.)
The router forwards the frame to all ports in the network and learns the address from the reply frame.
The destination host IP address is embedded in the DLCI.
The router searches Inverse ARP tables for maps of DLCIs to IP addresses.
A table of static mappings can be searched.
The router broadcasts a request for the required IP address.
35. Refer to the exhibit. From the output of the show interface commands, at which OSI layer is a fault indicated?
application
transport
network
data link
physical
36. Refer to the exhibit. The network administrator creates a standard access control list to prohibit traffic from the 192.168.1.0/24 network from reaching the 192.168.2.0/24 network while still permitting Internet access for all networks. On which router interface and in which direction should it be applied?
interface fa0/0/0, inbound
interface fa0/0/0, outbound
interface fa0/0/1, inbound
interface fa0/0/1, outbound
37. Refer to the exhibit. The SSH connections between the remote user and the server are failing. The correct configuration of NAT has been verified. What is the most likely cause of the problem?
SSH is unable to pass through NAT.
There are incorrect access control list entries.
The access list has the incorrect port number for SSH.
The ip helper command is required on S0/0/0 to allow inbound connections.
38. Refer to the exhibit. A technician issues the show interface s0/0/0 command on R1 while troubleshooting a network problem. What two conclusions can be determined by from the output shown? (Choose two.)
The bandwidth has been set to the value of a T1 line.
Encapsulation should of this inteface be changed to PPP.
There is no failure indicated in an OSI Layer 1 or Layer 2.
The physical connection between the two routers has failed.
The IP address of S0/0 is invalid, given the subnet mask being used.
39. Refer to the exhibit. A packet is being sent from Host A to Host B through the VPN tunnel between R1 and R3. When the packet first arrives at R3, what are the source and destination IP addresses of the packet?
Source 192.168.1.2 - Destination 192.168.4.2
Source 192.168.3.1 - Destination 192.168.3.2
Source 192.168.2.1 - Destination 192.168.3.2
Source 192.168.3.1 - Destination 192.168.4.2
40. An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
RIPng is incompatible with dual-stack technology.
All interfaces have been configured with the incorrect IPv4 addresses.
RIPv1 or RIPv2 needs to be configured in addition to RIPng to successfully use IPv4.
When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are shut down in favor of the newer technology.
41. Which wireless solution can provide mobile users with non line-of-sight broadband Internet access at speeds comparable to DSL or cable?
Wi-Fi
WiMAX
satellite
Metro Ethernet
42. A network administrator added two switches and a new VLAN over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Perform a baseline test and compare the current values to values that were obtained in previous weeks.
Interview departmental secretaries and determine if they think load time for web pages is improved.
Compare the hit counts on the company web server for the current week to the values that were recorded from previous weeks.
Performance on the intranet can be determined by monitoring load times of company web pages from remote sites.
43. Refer to the exhibit. The network administrator is adding R1 to an existing network. As a part of the corporate IT procedures, the administrator attempts to back up the router Cisco IOS software of R1 and receives the output shown. The network administrator then attempts unsuccessfully to ping the TFTP server from the console session. What should be done next to isolate this problem?
From R2, validate that interface Fa0/0 is operational.
From the TFTP server, verify that the software on the TFTP server is operational.
From the TFTP server, confirm there is enough room on the TFTP server for the Cisco IOS software.
From the console session, make sure that R1 has a route to the network where the TFTP server resides.
44. What functionality do access control lists provide when implementing dynamic NAT on a Cisco router?
defines which addresses can be translated
defines which addresses are assigned to a NAT pool
defines which addresses are allowed out of the router
defines which addresses can be accessed from the inside network
45. A network administrator is working with an applications team to fix a problem that a server based application is having with response time. The administrator has examined the network portions of the data path and identified several possible problem areas. The applications team has simultaneously identified potential issues with the current release of software. The network administrator begins addressing the network issues while the applications team implements software patches.
Which statement applies to this situation?
Changes to the network will reveal problems that are caused by the new patches.
Scheduling will be more difficult if the network and software teams work independently.
It will be difficult to isolate the problem if two teams are implementing changes independently.
Results from changes will be easier to reconcile and document if each team works in isolation.
46. Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 inside network. Host A has sent a packet to the web server. What is the destination IP address of the return packet from the web server?
10.1.1.2:1234
172.30.20.1:1234
172.30.20.1:3333
192.168.1.2:80
47. Which three guidelines would help contribute to creating a strong password policy? (Choose three.)
Once a good password is created, do not change it.
Deliberately misspell words when creating passwords.
Create passwords that are at least 8 characters in length.
Use combinations of upper case, lower case, and special characters.
Write passwords in locations that can be easily retrieved to avoid being locked out.
Use long words found in the dictionary to make passwords that are easy to remember.
48. What will be the result of adding the command ip dhcp excluded-address 172.16.4.1 172.16.4.5 to the configuration of a local router that has been configured as a DHCP server?
Traffic that is destined for 172.16.4.1 and 172.16.4.5 will be dropped by the router.
Traffic will not be routed from clients with addresses between 172.16.4.1 and 172.16.4.5.
The DHCP server function of the router will not issue the addresses between 172.16.4.1 and 172.16.4.5.
The router will ignore all traffic that comes from the DHCP servers with addresses 172.16.4.1 and 172.16.4.5.
49. Which two statements are true about IPv6? (Choose two.)
Security options are build into IPv6.
IPv6 addresses require less router overhead to process.
IPv6 can only be configured on an interface that does not have IPv4 on it.
There is no way to translate between IPv4 addresses and IPv6 addresses.
When enabled on a router, IPv6 can automatically configure link-local IPv6 addresses on all interfaces.
50. Refer to the exhibit. A network administrator has issued the commands that are shown on Router1 and Router2. A later review of the routing tables reveals that neither router is learning the LAN network of the neighbor router. What is most likely the problem with the RIPng configuration?
The serial interfaces are in different subnets.
The RIPng process is not enabled on interfaces.
The RIPng network command is not configured.
The RIPng processes do not match between Router1 and Router2.
51. At what physical location does the responsibilty for a WAN connection change from the user to the service provider?
demilitarized zone (DMZ)
demarcation point
local loop
cloud
52. Refer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP address from this DHCP server. The output of the debug ip dhcp server command shows "DHCPD: there is no address pool for 192.168.1.1". What is the problem?
The 192.168.1.1 address has not been excluded from the DHCP pool.
The pool of addresses for the 192Network pool is incorrect.
The default router for the 192Network pool is incorrect.
The 192.168.1.1 address is already configured on Fa0/0.
53. Which three functions are provided by the Local Management Interface used in Frame Relay networks? (Choose three.)
exchange information about the status of virtual circuits
map DLCIs to network addresses
provide flow control
provide error notification
provide congestion notification
send keepalive packets to verify operation of the PVC
54. Which three items are LCP options that can be configured for PPP? (Choose three.)
CHAP
Stacker
IPCP
CDPCP
Multilink
55. What are two main components of data confidentiality? (Choose two.)
checksum
digital certificates
encapsulation
encryption
http://www.ccna4u.info
Thứ Sáu, 24 tháng 10, 2008
CCNA4 Module 5 ACLs(100%)
CCNA4 v 4.0 Exam chapter 5 ACLs
1. By default, how is IP traffic filtered in a Cisco router?
| blocked in and out of all interfaces |
| blocked on all inbound interfaces, but permitted on all outbound interfaces |
| permitted in and out of all interfaces |
| blocked on all outbound interfaces, but permitted on all inbound interfaces |
2. Which three parameters can ACLs use to filter traffic? (Choose three.)
| packet size |
| protocol suite |
| source address |
| destination address |
| source router interface |
| destination router interface |
3. How do Cisco standard ACLs filter traffic?
| by destination UDP port |
| by protocol type |
| by source IP address |
| by source UDP port |
| by destination IP address |
4. Which two statements are correct about extended ACLs? (Choose two)
| Extended ACLs use a number range from 1-99. |
| Extended ACLs end with an implicit permit statement. |
| Extended ACLs evaluate the source and destination addresses. |
| Port numbers can be used to add greater definition to an ACL. |
| Multiple ACLs can be placed on the same interface as long as they are in the same direction. |
5. Where should a standard access control list be placed?
| close to the source |
| close to the destination |
| on an Ethernet port |
| on a serial port |
6. Which three statements describe ACL processing of packets? (Choose three.)
| An implicit deny any rejects any packet that does not match any ACL statement. |
| A packet can either be rejected or forwarded as directed by the statement that is matched. |
| A packet that has been denied by one statement can be permitted by a subsequent statement. |
| A packet that does not match the conditions of any ACL statements will be forwarded by default. |
| Each statement is checked only until a match is detected or until the end of the ACL statement list. |
| Each packet is compared to the conditions of every statement in the ACL before a forwarding decision is made. |
7. Which two statements are true regarding the significance of the access control list wildcard mask 0.0.0.7? (Choose two.)
| The first 29 bits of a given IP address will be ignored. |
| The last 3 bits of a given IP address will be ignored. |
| The first 32 bits of a given IP address will be checked. |
| The first 29 bits of a given IP address will be checked. |
| The last 3 bits of a given IP address will be checked. |
8. Which two statements are true regarding the following extended ACL? (Choose two.)
access-list 101 deny tcp 172.16.3.0 0.0.0.255 any eq 20
access-list 101 deny tcp 172.16.3.0 0.0.0.255 any eq 21
access-list 101 permit ip any any
| FTP traffic originating from network 172.16.3.0/24 is denied. |
| All traffic is implicitly denied. |
| FTP traffic destined for the 172.16.3.0/24 network is denied. |
| Telnet traffic originating on network 172.16.3.0/24 is denied. |
| Web traffic originating from 172.16.3.0 is permitted. |
9. Interface s0/0/0 already has an IP ACL applied inbound. What happens when the network administrator attempts to apply a second inbound IP ACL?
| The second ACL is applied to the interface, replacing the first. |
| Both ACLs are applied to the interface. |
| The network administrator receives an error. |
| Only the first ACL remains applied to the interface. |
10. Refer to the exhibit. When creating an extended ACL to deny traffic from the 192.168.30.0 network destined for the Web server 209.165.201.30, where is the best location for applying the ACL?
| ISP Fa0/0 outbound |
| R2 S0/0/1 inbound |
| R3 Fa0/0 inbound |
| R3 S0/0/1 outbound |
11. Which two statements are true regarding named ACLs? (Choose two.)
| Only named ACLs allow comments. |
| Names can be used to help identify the function of the ACL. |
| Named ACLs offer more specific filtering options than numbered ACLs. |
| Certain complex ACLs, such as reflexive ACLs, must be defined with named ACLs. |
| More than one named IP ACL can be configured in each direction on a router interface. |
12. Which three items must be configured before a dynamic ACL can become active on a router? (Choose three.)
| extended ACL |
| reflexive ACL |
| console logging |
| authentication |
| Telnet connectivity |
| user account with a privilege level of 15 |
13. Refer to the exhibit. How does this access list process a packet with the source address 10.1.1.1 and a destination of 192.168.10.13?
| It is allowed because of the implicit deny any. |
| It is dropped because it does not match any of the items in the ACL. |
| It is allowed because line 10 of the ACL allows packets to 192.168.0.0/16. |
| It is allowed because line 20 of the ACL allows packets to the host 192.168.10.13. |
14. A network administrator needs to allow traffic through the firewall router for sessions that originate from within the company network, but the administrator must block traffic for sessions that originate outside the network of the company. What type of ACL is most appropriate?
| dynamic |
| port-based |
| reflexive |
| time-based |
15. Refer to the exhibit. How will Router1 treat traffic matching the time-range requirement of EVERYOTHERDAY?
| TCP traffic entering fa0/0 from 172.16.1.254/24 destined to the 10.1.1.0/24 network is permitted. |
| TCP traffic entering fa0/0 from 10.1.1.254/24 destined to the 172.16.1.0/24 network is permitted. |
| Telnet traffic entering fa0/0 from 172.16.1.254/24 destined to the 10.1.1.0/24 network is permitted. |
| Telnet traffic entering fa0/0 from 10.1.1.254/24 destined to the 172.16.1.0/24 network is permitted. |
16. The following commands were entered on a router:
Router(config)# access-list 2 deny 172.16.5.24
Router(config)# access-list 2 permit any
The ACL is correctly applied to an interface. What can be concluded about this set of commands?
| The wildcard mask 0.0.0.0 is assumed. |
| The access list statements are misconfigured. |
| All nodes on the 172.16.0.0 network will be denied access to other networks. |
| No traffic will be allowed to access any nodes or services on the 172.16.0.0 network. |
17. Refer to the exhibit. The administrator wishes to block web traffic from 192.168.1.50 from reaching the default port of the web service on 192.168.3.30. To do this, the access control list name is applied inbound on the router R1 LAN interface. After testing the list, the administrator has noted that the web traffic remains successful. Why is web traffic reaching the destination?
| Web traffic does not use port 80 by default. |
| The access list is applied in the wrong direction. |
| The access list needs to be placed closer to the destination, on R3. |
| The range of source addresses specified in line 10 does not include host 192.168.1.50. |
18. Refer to the exhibit. What will be the effect of the configuration that is shown?
| Users attempting to access hosts in the 192.168.30.0/24 network will be required to telnet to R3. |
| Hosts connecting to resources in the 191.68.30.0/24 network have an idle timeout of 15 minutes. |
| Anyone attempting to telnet into R3 will have an absolute time limit of five minutes. |
| Telnet access to R3 will only be permitted on Serial 0/0/1. |
19. Which statement about standard ACLs is true
| Standard ACLS must be numbered and cannot be named. |
| They should be placed as close to the destination as possible. |
| They can filter based on source and destination address as well as on source and destination port. |
| When applied to an outbound interface, incoming packets are processed before they are routed to the outbound interface. |
20. Which benefit does an extended ACL offer over a standard ACL?
| Extended ACLs can be named, but standard ACLs cannot. |
| Unlike standard ACLs, extended ACLS can be applied in the inbound or outbound direction. |
| Based on payload content, an extended ACL can filter packets, such as information in an e-mail or instant message. |
| In addition to the source address, an extended ACL can also filter on destination address, destination port, and source port. |
21. Which feature will require the use of a named ACL rather than a numbered ACL?
| the ability to filter traffic based on a specific protocol |
| the ability to filter traffic based on an entire protocol suite and destination |
| the ability to specify source and destination addresses to use when identifying traffic |
| the ability to edit the ACL and add additional statements in the middle of the list without removing and re-creating the list |
22. A technician is creating an ACL and needs a way to indicate only the subnet 172.16.16.0/21. Which combination of network address and wildcard mask will accomplish the desired task?
| 172.16.0.0 0.0.255.255 |
| 127.16.16.0 0.0.0.255 |
| 172.16.16.0 0.0.7.255 |
| 172.16.16.0 0.0.15.255 |
| 172.16.16.0 0.0.255.255 |
23. Which two statements accurately describe the characteristics of wildcard masks in an ACL? (Choose two.)
| Wildcard masks are the inverse of the subnet mask. |
| The word "any" indicates that all corresponding bits must be matched. |
| The word "host" corresponds to a wildcard mask of 0.0.0.0 in an ACL statement. |
| A wildcard mask of 0.0.255.255 can be used to create a match for an entire Class B network. |
| A wildcard mask bit of 1 indicates that the corresponding bit in the address must be matched. |
24. Refer to the exhibit. Which statement is true about ACL 110 if ACL 110 is applied in the inbound direction on S0/0/0 of R1?
| It will deny TCP traffic to the Internet if the traffic is sourced from the 172.22.10.0/24 network. |
| It will not allow TCP traffic coming from the Internet to enter the network 172.22.10.0/24. |
| It will allow any TCP traffic from the Internet to enter the network 172.22.10.0/24. |
| It will permit any TCP traffic that originated from network 172.22.10.0/24 to return inbound on the S0/0/0 interface. |
25. Refer to the exhibit. ACL 120 is configured inbound on the serial0/0/0 interface on router R1, but the hosts on network 172.11.10.0/24 are able to telnet to network 10.10.0.0/16. On the basis of the provided configuration, what should be done to remedy the problem?
| Apply the ACL outbound on the serial0/0/0 interface on router R1. |
| Apply the ACL outbound on the FastEthernet0/0 interface on router R1. |
| Include the established keyword at the end of the first line in the ACL. |
| Include a statement in the ACL to deny the UDP traffic that originates from 172.11.10.0/24 network. |
26. Refer to the exhibit. The network administrator applied an ACL outbound on S0/0/0 on router R1. Immediately after the administrator did so, the users on network 172.22.30.0/24 started complaining that they have intermittent access to the resources available on the server on the 10.10.0.0/16 network. On the basis of the configuration that is provided, what is the possible reason for the problem?
| The ACL allows only the mail traffic to the server; the rest of the traffic is blocked. |
| The ACL permits the IP packets for users on network 172.22.30.0/24 only during a specific time range. |
| The ACL permits TCP packets only if a connection is established from the server to the network 172.22.0.0/16. |
| The ACL allows only TCP traffic from users on network 172.22.40.0/24 to access the server; TCP traffic from any other sources is blocked. |
CCNA4 MODULE 3 (Update 28/12/08)
download 100/100 (Update 28/12/08)
CCNA4 v 4.0 Exam chapter 3 Frame Relay
1. Which best describes the benefit of using Frame Relay as opposed to a leased line or ISDN service?
| | Customers can define their virtual circuit needs in far greater combinations, with increments as small as 64 kbps. |
| | Customers pay for an end-to-end connection that includes the local loop and the network link. |
| | Customers only pay for the local loop and the bandwidth they purchase from the network provider. |
| | Connecting new sites requires new lower cost circuit installations when compared to ISDN dialup costs or adding additional hardware for leased service. |
2. What two methods does Frame Relay technology use to process frames that contain errors? (Choose two.)
| | Frame Relay services depend on the upper layer protocols to handle error recovery. |
| | It requires the receiving device to request that the sender retransmit erroneous frames. |
| | FECN, BECN, and DE bits are set in the frames to minimize errors. |
| | The receiving device drops any frames that contain errors without notifying the sender. |
| | The frame relay switch notifies the sender that errors were detected. |
3. What best describes the use of a data-link connection identifier (DLCI)?
| | local address identifying a destination router across a Frame Relay network |
| | locally significant address used to identify a virtual circuit |
| | logical address identifying the interface between a router and a Frame Relay switch |
| | logical address used to identify the DCE |
4. What is created between two DTEs in a Frame Relay network?
| | ISDN circuit |
| | limited access circuit |
| | switched parallel circuit |
| | virtual circuit |
5. Which two items allow the router to map data link layer addresses to network layer addresses in a Frame Relay network? (Choose two.)
| | ARP |
| | RARP |
| | Proxy ARP |
| | Inverse ARP |
| | LMI status messages |
| | ICMP |
6. Refer to the exhibit. A ping is sent to address 192.168.50.10 from the Peanut router. Which DLCI will be used to send the ping?

| | 110 |
| | 115 |
| | 220 |
| | 225 |
7. Refer to the exhibit. Which two outcomes occur from the configuration shown? (Choose two.)

| | The broadcasts will be forwarded to 10.1.1.1. |
| | The router will use DLCI 22 to forward data to 10.1.1.1. |
| | DLCI 22 will replace the MAC address in the ARP table for entry 10.1.1.1 |
| | Frames arriving on interface serial 0/0/0 of RT_1 will have a data link layer address of 22. |
| | Inverse-ARP will now add an entry for 10.1.1.1 into the Frame Relay map table using DLCI 22. |
8. Refer to the exhibit. What effect does the point-to-point configuration on subinterface S0/0.110 have on the operation of the router?

| | It helps to conserve IP addresses. |
| | It establishes multiple PVC connections to multiple physical interfaces. |
| | It eliminates split horizon issues without increasing the likelihood of routing loops. |
| | It requires the configuration of the encapsulation command on the subinterface. |
9. Which three actions does a Frame Relay switch perform when it detects an excessive build-up of frames in its queue? (Choose three.)
| | puts a hold on accepting frames in excess of the CIR |
| | drops frames from the queue that have the DE bit set |
| | reduces the number of frames it sends over the link |
| | re-negotiates flow control with the connected device |
| | sets the FECN bit on all frames it receives on the congested link |
| | sets the BECN bit on all frames it places on the congested link |
10. Refer to the exhibit. Which two statements are true given the output shown? (Choose two.)

| | The IP address of the local Frame Relay interface is 172.16.1.4. |
| | The local DLCI number is 401. |
| | Inverse ARP is being used on this connection. |
| | This interface is in the active state and in the process of negotiating configuration parameters. |
| | Multicast is not enabled on this connection. |
11. Refer to the exhibit. When troubleshooting a Frame Relay connection, an administrator entered the show interfaces s0/0 command and received the output shown in the exhibit. What are two probable reasons for this problem? (Choose two.)

| | The cable between the CSU/DSU and the router is disconnected. |
| | The serial 0/0 interface is shutdown. |
| | The router is not configured for the same Frame Relay PVC as the switch. |
| | The LMI type on the Frame Relay switch is NOT ANSI. |
| | The address of the Frame Relay switch is not in the routing table. |
12. Refer to the exhibit. What can be determined about the Frame Relay switch from the output shown?

| | It is currently not transmitting data. |
| | It is in the process of establishing the PVC. |
| | It has put a hold on processing frames in excess of the CIR. |
| | It is experiencing congestion. |
13. Refer to the exhibit. Router R2 is part of a Frame Relay network that uses OSPF for IP routing. After the commands that are shown are entered, R2 will not exchange OSPF information correctly. What is the likely cause?

| | The frame-relay map command requires the broadcast keyword. |
| | The DLCIs on each end of the PVCs are not identical. |
| | The R2 S0/0/0 interface has not been brought online. |
| | The LMI or Inverse ARP or both are not working. |
14. Which statement about Frame Relay subinterfaces is correct?
| | Multipoint interfaces will automatically forward routing broadcasts but will consume more IP addresses than point-to-point subinterfaces will consume. |
| | Point-to-point subinterfaces act like leased lines and eliminate split-horizon routing issues. |
| | Interfaces with multiple PVCs require a separate subinterface for each PVC. |
| | Multipoint configurations cannot use subinterfaces. |
15. Refer to the exhibit. You are a network administrator who has been tasked with completing the Frame Relay topology that interconnects two remote sites. Router HQ belongs to both the 172.16.1.0/24 and 172.16.2.0/24 subnets with IP addresses of 172.16.1.3 and 172.16.2.3 respectively. Traffic between R1 and R2 must travel through HQ first. How should the serial interface on HQ be configured to complete the topology?

| | one multipoint subinterface |
| | two point-to-point subinterfaces |
| | with the physical interface configured with two ip addresses |
| | one IP address on a point-to-point subinterface and one IP address on the physical interface |
16. What consideration must be taken into account if RIP is used on Frame Relay multiaccess networks?
| | To forward routing updates, address-to-DLCI mapping must be done via the use of the frame-relay map command coupled with the broadcast keyword. |
| | Inverse ARP must be enabled to turn routing update broadcasts into unicast traffic that can be propagated to other Frame Relay nodes. |
| | Because broadcast traffic is not supported, RIPv1 cannot be implemented on Frame Relay networks. |
| | To forward broadcast routing updates, dynamic mapping must be enabled. |
17. Refer to the exhibit. Which statement explains why the Frame Relay connection between R1 and R2 is failing?

| | Split horizon must be disabled. |
| | The LMI type must be specified. |
| | Logical subinterfaces must be used instead. |
| | The frame-relay map commands are using incorrect DLCIs. |
18. Refer to the exhibit. Router R1 has been configured for Frame Relay connectivity to routers R2 and R3. Which set of configuration options for routers R2 and R3 would provide each router connectivity to R1?

| | R2(config)# interface serial0/0/1 |
| | R2(config)# interface serial0/0/1 |
| | R2(config)# interface serial0/0/1.201 point-to-point |
| | R2(config)# interface serial0/0/1.201 point-to-point |
19. Refer to the exhibit. What can be known about the configuration of router R1 from the output?

| | The Frame Relay LMI DLCI has been incorrectly configured as DLCI 1023. |
| | The Frame Relay LMI type has been changed from its default. |
| | The Serial 0/0/0 interface has been configured as a data communications equipment device. |
| | The command encapsulation frame-relay ietf has been used on the Serial 0/0/0 interface. |
20. Refer to the exhibit. What can be determined about the configuration of router R1 from the exhibited output?

| | LMI updates are not being received properly. |
| | The LMI type for the Serial 0/0/0 interface has been left to its default configuration. |
| | Cisco HDLC is used as a Layer 2 encapsulation protocol on the Serial 0/0/0 interface. |
| | The Serial 0/0/0 interface has been configured as a data communications equipment device. |
21. Refer to the exhibit. What can be determined from the output?

| | Serial 0/0/0 has been configured with an DLCI of 201. |
| | Serial 0/0/0 has the feature frame-relay inverse-arp enabled. |
| | Serial 0/0/0 has been configured with an IP address of 172.16.4.3. |
| | Serial 0/0/0 has been configured with the command frame-relay map ip 172.16.4.3 201 broadcast. |
22. Refer to the exhibit. Router R1 has been configured for Frame Relay connectivity to routers R2 and R3. What configuration option should be configured on the R2 and R3 serial interfaces in order for all routers to ping each other successfully?

| | R2(config-if)# frame-relay interface-dlci 201 broadcast |
| | R2(config-if)# frame-relay map ip 10.1.1.1 201 broadcast |
| | R2(config-if)# frame-relay map ip 10.1.1.3 201 broadcast |
| | R2(config-if)# frame-relay map ip 10.1.1.1 201 broadcast |